Patterns
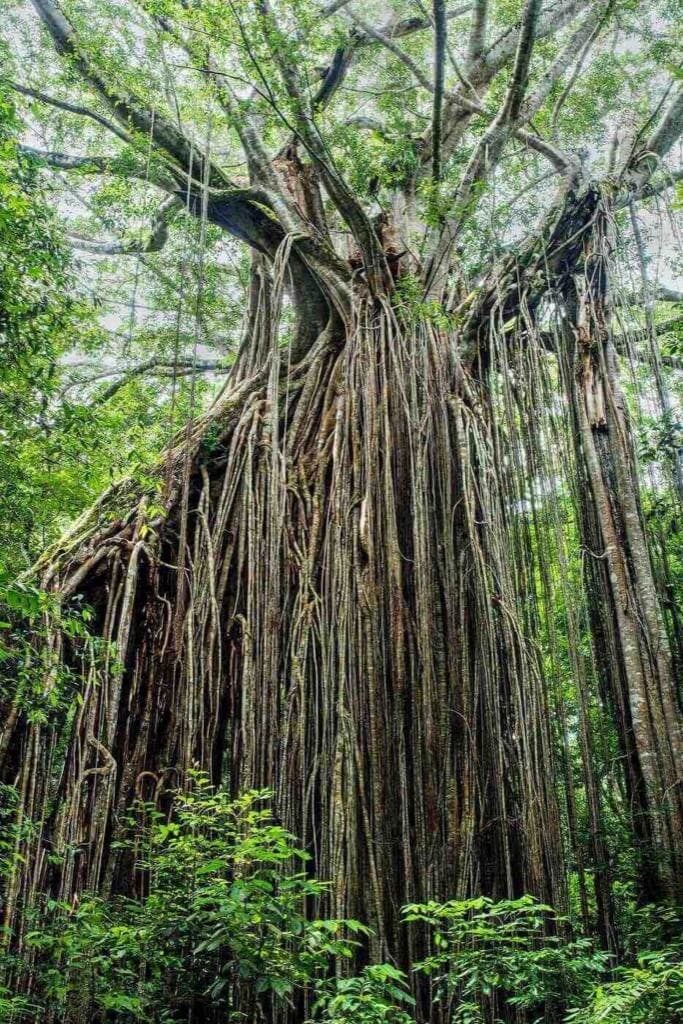
Branch by Abstraction Pattern
The strangler pattern is useful for scenarios where you can intercept the calls at the edge of your monolithic application. But what do you do in a scenario where the functionality you're trying to extract is not called directly from the outside, rather it is being called from multiple other places inside the monolith?
·5 min read